The reality for many businesses is a delayed discovery of security breaches. Network Breach Detection's innovative approach changes this narrative. Our solution requires just three minutes to set up, demands no continual management, and boasts almost no false positives. This efficiency enables you to identify potential threats well before they become entrenched. Discover how our Network Breach Detection Sensors, whether in hardware, virtual machine, or cloud-based formats, are effectively deployed to enhance your network's security.
Powered by Thinkst Canary
Tons of security products would be useful, if only you changed everything you did and made them the centre of your universe. This never happens, so they sit half deployed forever.
Network Breach Detection doesn’t try to monopolise your time or dominate your thinking. Deploy your birds and forget about them. We will remain silent until you need us most… One alert.
When it matters!
Set up and deploy Canary sensors effortlessly throughout your network infrastructure. Choose from a range of formats—be it hardware, virtual, or cloud-based. Configure each unit to impersonate different network components. For example, one could mimic a Windows file server, another a network router, or several as Linux web servers. These units are expertly crafted to offer realistic services and convincingly imitate the systems they represent. Once deployed, they blend seamlessly into your network. Operating unobtrusively in the background, they are primed to detect unauthorized intrusions. Attackers typically search for high-value targets within a network. They may probe Active Directory for file servers, sift through file shares for sensitive documents, try well-known passwords on network devices and web services, or scan for unguarded services across the network. When these intruders interact with a Canary sensor, the carefully curated, authentic-looking services are designed to draw them in. This interaction is the trap – as soon as they engage, they expose their presence, activating an alert from the unit. This immediate notification system ensures you are promptly informed of any security breach.
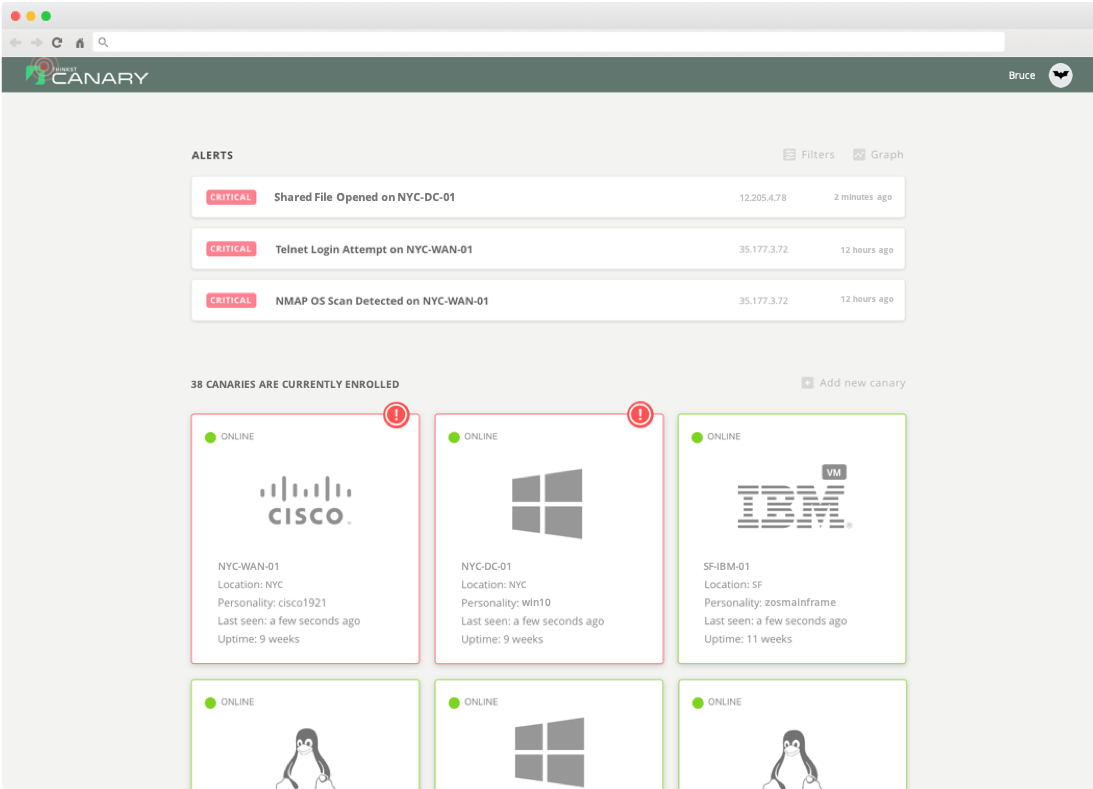
Every client is provided with a dedicated, hosted management console. This platform is your command center for configuring settings and managing your Network Breach Detection units. It's designed for efficiency and ease of use. Network Breach Detection units continuously update their status to your console, offering real-time reporting. However, this doesn't add to your screen fatigue – it's not a system that demands constant attention. Even clients with a substantial deployment of units typically experience only a few notable events annually. In the event of an incident, you'll be promptly alerted through your preferred channel, be it email, text message, Slack notification, webhook, or traditional syslog. This ensures that you stay informed without the need for continuous monitoring.

Consider a scenario where an attacker has compromised a user in your organization and has been silently reading through company communications. Would you be aware of such a breach? Or imagine if your lead developer's system was targeted and compromised, perhaps at a public Wi-Fi hotspot. How quickly would you notice this security incident? This is where Canarytokens come into play. Deploy fake AWS-API keys on every enterprise laptop as one of many strategies. Attackers infiltrating your systems are likely to use these keys, unwittingly alerting you to their presence. But Canarytokens' utility extends beyond just API keys. They can be embedded in various forms like web URLs, email addresses, or even documents. If an intruder accesses a document or uses a tokenized email address, you get an alert. They serve as nuanced tripwires across your digital landscape. Canarytokens are trivial to deploy but provide a high-quality signal. Their versatility means you can place these tokens in numerous settings - from server files to cloud storage, offering broad coverage and early detection of a wide range of intrusion tactics.